Blog
The latest news and insights from the UK’s deepest and broadest knowledge base of educational expertise.
Topic
All
Curriculum & Assessment
HR & Development
School Websites
HR Guidance
Risk & Governance
Finance & Payroll
Training
Assessment & Reporting
CPD
MAT
Parent Engagement
Parental Engagement
Communications
Finance Guidance
Infant Schools
EYFS Schools
Education Resources
MAT Websites
Primary
School MIS
Secondary
Progress Data
Safeguarding
Staff Well-being
Embracing change: The evolution of Primary School assessment in England
Introduction Over the last decade, primary school assessment in England has undergone significant transformations, influenced by policy changes, educational technology advancements, and a shift towards more dynamic teaching methodologies. This.
Juniper Education 15 April, 2024
All articles
Understanding DBS checks in schools: Who needs them and why
Jo Garner 28 March, 2024
How to improve parental engagement in schools for separated families
Juniper Education 26 March, 2024
Maintain Website Compliance and Stay Ready for Ofsted Inspections
Juniper Education 26 March, 2024
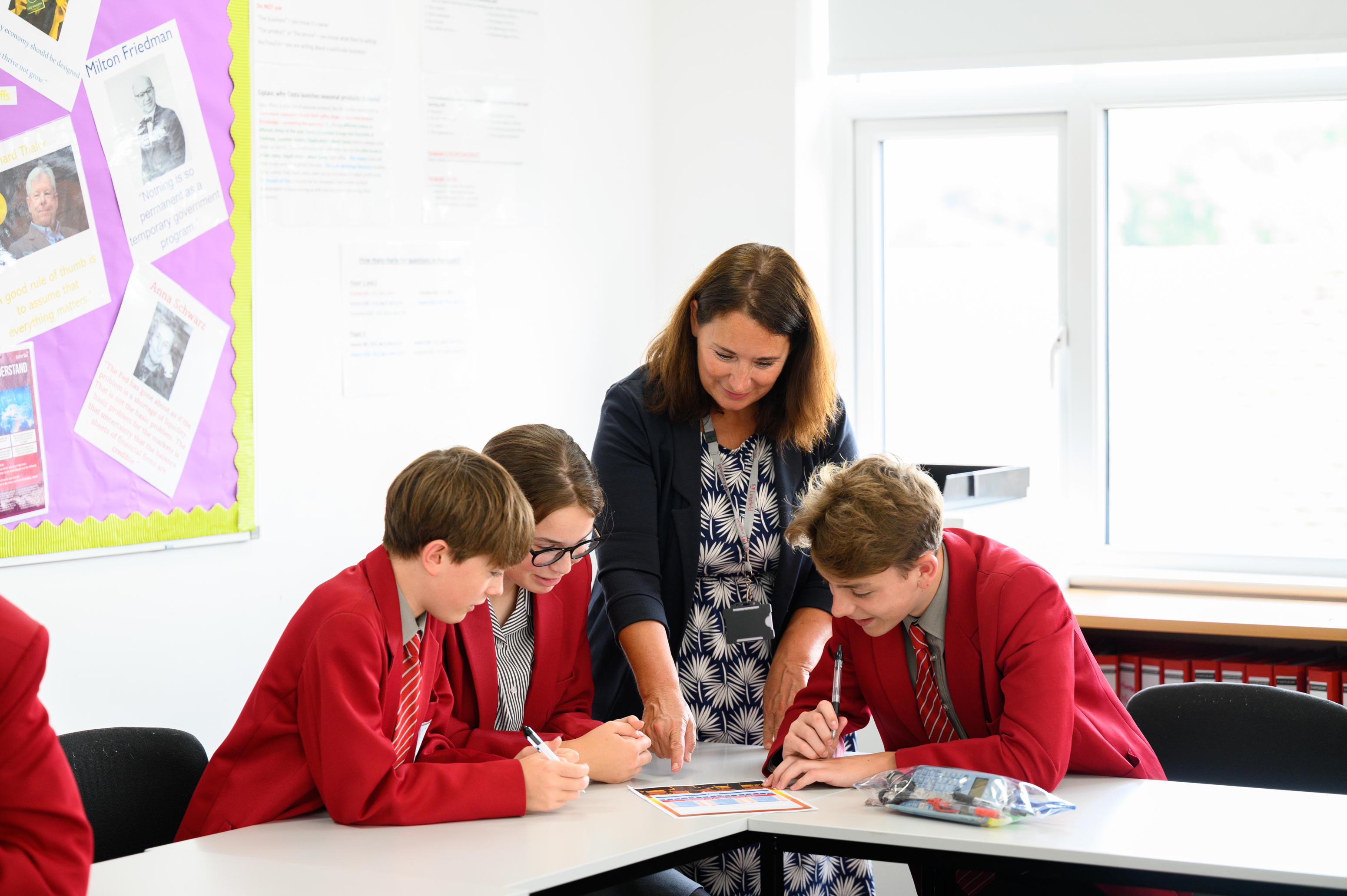
Developing spoken language skills in the classroom

Kathy Ewers 25 March, 2024
Everything You Need to Know About Hiring Teachers from Overseas

Nicki Harris 21 March, 2024
How to Produce Quality Content for a School Website
Juniper Education 19 March, 2024
How to develop fluent transcription skills in school

Kathy Ewers 14 March, 2024
Stay in the loop
Subscribe to get our latest resources straight to your inbox.